SMART MOBILITY AND THE BLOCKCHAIN
Everyone has heard of Bitcoin and there are some specific use-cases emerging that use its underlying technology, the blockchain. These include supply chain management and logistics, property ownership and voting. There are also enterprise applications being developed for smart cars, smart energy, health trackers, and peer-to-peer transactions.
One area we will explore in this post is digital identity.
First, here’s a quick reminder on the blockchain concept. It’s a method for recording transactional information on a distributed ledger where encrypted records are not kept by a single party. Instead everything is decentralized, meaning that members of the service validate and record all transactions. It also operates by consensus, and if an agreed percentage of the network approves a transaction it is then validated and recorded. It is thought the oversight of everyone being involved via the blockchain adds trust to proceedings.
Blockchain technology enables different parties that don’t necessarily know or trust each other to securely exchange value or assets over the internet without involving a third party.
Work is well underway to bring blockchain services to market. In the main, the technology promises to:
1. Automate processes – replacing manual work and eliminating human error
2. Provide transparency – all transactions are recorded and shared by the blockchain community
3. Ensure transactions are immutable—once written, they can’t be changed


Smart Mobility – a blockchain example for car-sharing services
Currently car-renting services are hailed by a smartphone app. This model isn’t much different to how we use taxis today. But soon there will be peer-to-peer (P2P) car sharing services where car owners will let others drive their car (for example Drivy). Collective ride sharing and car-pooling is also going to grow in popularity as new services are launched.
It is clear that trust will be central to this P2P model where people are letting others drive their cars. If you are going to opt into something like this, you will have to trust the identity of other drivers, their ability and eligibility to drive, and also the condition of the cars.
Building trust in a P2P model is at least twice as hard as doing business with an established company. In this regard, a consortium blockchain approach that combines multiple sources could work to verify drivers, removing the need for a so called ‘leap of faith’ from users. The technology underpinning the platform would be able to provide the trust that every driver can legally drive and every car is roadworthy.
For this to work seamlessly, a number of different players would be part of this ecosystem. These would include the car sharing service provider (which could be a car manufacturer), insurance companies, MNOs, OEMs, banks, and governments.
Let’s examine how this could work from the perspective of a driver:
Enrollment request through a mobile app
The first step would be downloading the car sharing app from a provider. This provider could be a MNO, an OEM, a car manufacturer, or a bank.
Approval process through the ledger
During the enrollment stage, these parties would verify the identity of the drivers by assessing the authenticity and validity of the driver’s ID documents and making sure the driver is the rightful owner of her/his ID documents. Once verified, these proofs would be published to a distributed blockchain ledger. Insurance companies could add other attributes to those proofs, such as details on a user’s driving history.
Once enough material has been uploaded, it would be analyzed to form a consensus on the driver’s identity and ability to legally drive. If approved, the clearance for the driver would also be recorded on the distributed ledger, as a smart proof.
Service usage by authorized drivers
At this point approved drivers would receive their authentication credentials, downloaded onto their mobile device. Each credential would take the form of a digital identity: a collection of electronic identity attributes including biographic and biometric data.
Then each time a driver requests a car sharing service, he or she would be verified through the distributed ledger, in real-time, using his/her digital ID and the nearest car available would be displayed on their mobile device. They could then unlock the chosen car with their digital ID.
Is this consortium blockchain secure?
Generally speaking the blockchain approach makes it very difficult to cheat the system. Fraud and unauthorized manipulation of data are difficult because it is very hard to fake your credentials across multiple secure touchpoints.
However, it is important to note that a blockchain is not secure by default, unless the blockchain is secured. And this is why this nascent technology needs to abide by the following fundamental principles:
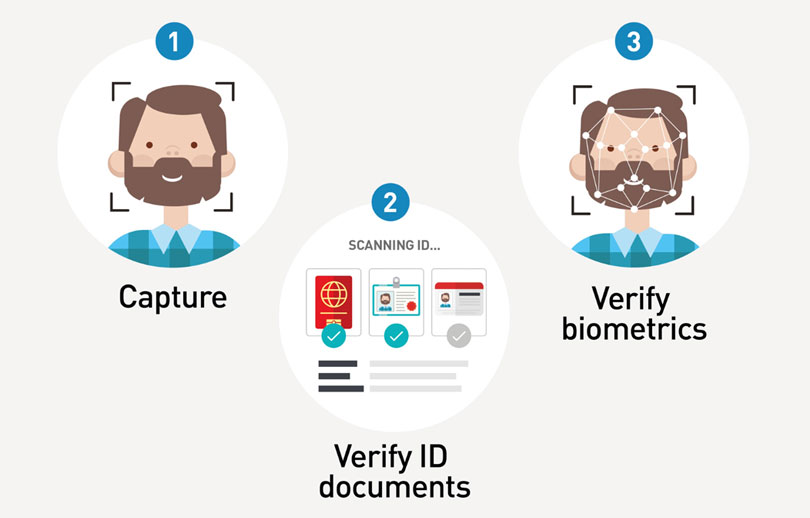
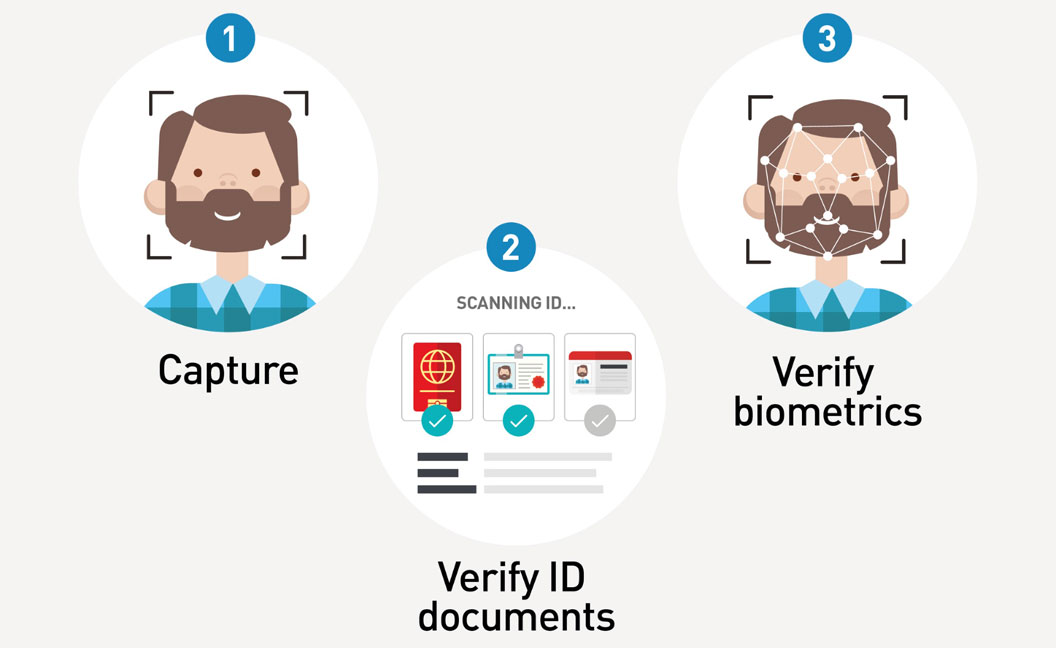
Secure enrollment process
We must trust in the enrollment processes of drivers. And there are still questions to answer.
Who is the authority performing such verification? Is it trusted? Is the driving license verification process trustworthy? How and where does it take place?
If this verification process has security issues, wrong proofs could be stored everywhere in the distributed ledger.
In this regard, Trusted Digital Identity services can be used to orchestrate the enrollment processes. Typically, MNOs, OEMs, banks, and of course governments could play the de facto the role of verifying identities, as this is part of their regular activities today.
Secure credential management
We must trust in the smart proofs stored in the distributed ledger so that they aren’t corrupted. We also need to make sure that the information stored in the cloud is anonymous so that all information—such as the location of drivers—is kept private for data protection concerns (e.g. GDPR). Technologies such as data encryption and key management solutions like hardware security modules (HSMs) involving cryptography are ideally suited for this purpose.
We must also be able to trust in the mobile devices used to store the authentication credentials, so that they can’t be disclosed and copied. Tamper proof secure elements such as SIM and eSIMs, are ideally suited for this purpose. Typically, MNOs and OEMs are well-positioned for the issuance and management of such credentials as this is already part of their regular activities.
Secure authentication procedures
For authentication purposes, seamless and secure techniques involving biometry & liveness detection ensure that mobile devices cannot be used by anyone but the drivers themselves.
Major players have started investigating such technology. For example, the newly formed MOBI foundation by major manufacturers such as BMW, Ford, General Motors and Bosch is promoting standards in blockchain, distributed ledgers, and related technologies for the benefit of the mobility industry, consumers and communities.
Current technical and business hurdles to address
Indeed Blockchain relies on existing technology and is still nascent: there are many hurdles still to be addressed from a technical standpoint, in terms of scalability and computing resources for the blockchain. For instance, currently only seven Bitcoin transactions can be recorded per second, compared with thousands of transactions in established payment networks.
There are also issues in the permanence of the blockchain. Once a transaction is recorded it is immutable and cannot be erased. This may encroach people’s right to be forgotten.
Also, there are needs for greater clarification between how service providers can encourage end-users and businesses to participate in blockchain services that need to be running at all times. This is ultimately a case of evolving business models that will likely be addressed in the coming years.
Last but not least, when it comes to regulations and identity with the use of blockchain there are still many live discussions, as stated in this GSMA white paper. Some experts believe blockchains are an implementation choice and specific legislation and regulations are not needed, whereas other experts believe in an enforceable governance model for the identity lifecycle management for blockchain solutions. This means that further investigation is needed and frameworks developed which would meet GDPR legal requirements.
Author: Didier Benkoel-Adechy