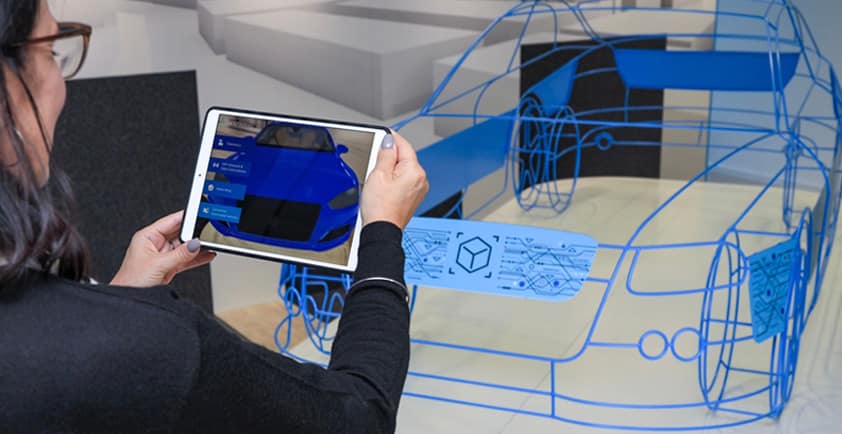
THE FUTURE OF CYBERSECURITY FOR CONNECTED CARS
Connected cars have slowly become mainstream, with more than 700 million of them expected to be operating on roads by 2030. Most new vehicles are leaving production lines with a host of features that require a connection to the online world, including GPS, lane assistance, collision avoidance, and modern infotainment systems. However, while connected vehicles offer abundant opportunities for the consumer, automakers need to seriously consider what they mean for consumer privacy and security. Any software vulnerabilities could undermine the safety of connected car systems and features, putting the user's sensitive information at risk as well as their physical safety. As such, automakers need to adopt a cybersecurity culture that not only addresses the obvious exposures in their vehicle's software, but other hidden vulnerabilities that could arise from third-party components in their vehicles.
The current state of cybersecurity in connected vehicles
Cybersecurity is still an unstandardized anomaly in the automotive industry. According to a report by the Ponemon Institute, software security is moving at a much slower pace than technology in the industry, with only 10 percent of automakers having an established cybersecurity team. The economies of cybersecurity in cars are inherently unfair; with the right tools, attacks are affordable, low-effort affairs.
On the other hand, mounting a coherent defense against such attacks requires higher effort and investment. So far, the playing field is in favor of the attackers, and there have been a few incidents that have put this into perspective. For example, security researchers demonstrated that a Jeep Cherokee could be hacked when they took control of the wipers, air conditioning, brakes, and accelerator from 10 miles away. Some Tesla vehicles also had a vulnerability that could potentially allow hackers to start the vehicle or cut the motor remotely.
The role of automakers in improving cybersecurity
Automakers must start viewing security testing as an investment that will result in better quality vehicles, not as an expense with no direct payback. Since technical vulnerabilities can arise at any time, automotive players need to consider cybersecurity throughout the product life cycle, starting from the design stage. Carmakers must include cybersecurity in design from the start since the complex supply chains and long development cycles of vehicle platforms do not allow for architectural changes in the late stages.
Beyond this, automakers must also ramp up their capabilities and expertise to monitor the cybersecurity of vehicles on the road. Since new threats can arise at any time, cybersecurity needs to be treated like other common servicing issues like changing the engine oil or replacing the spark plugs. Consumers should be able to get security-related software updates regularly well into the vehicle's ownership life cycle to ensure that they can deal with new and evolving cyber threats.
Regulatory change in cybersecurity is needed
Although regulatory bodies have a long way to go in ensuring that all vehicles operating on the roads have adequate cybersecurity systems to keep everyone safe, some have already taken a few steps in the right direction. For example, California now requires autonomous cars to meet industry standards for cybersecurity. The United Nations Economic Commission for Europe (UNECE) is also expected to finalize its regulations on cybersecurity and software updates, making cybersecurity a requirement for future vehicle sales. Industry experts see the UNECE regulation as the beginning of a new age of technical compliance regulation to address the increase of software and connectivity in the automotive industry.
Sensing an opportunity, cybercriminals are focusing more energy on attacking connected vehicles, posing a challenge for different players in the automotive industry. It is up to regulatory bodies to increase pressure on automakers to ensure that every vehicle that leaves the production line has better protection against current and future attacks.
Author: Karoline Gore